Government OT cybersecurity has become one of the most urgent priorities in public sector technology management. Operational technology networks powering water treatment plants, traffic management systems, power grids, and municipal buildings were built for reliability — not resilience against modern cyber threats. As adversaries increasingly target critical infrastructure, agencies that delay securing their SCADA and ICS environments face cascading consequences: service disruptions, public safety risks, and regulatory penalties. Book a demo to see how iFactory's OT security platform maps directly to your municipal infrastructure environment.
OT NETWORK PROTECTION PLATFORM
Secure Every Government OT Network From One Platform.
SCADA security, IoT device protection, and network segmentation purpose-built for municipal and public infrastructure environments.
Why Government OT Networks Are the Most Vulnerable Attack Surface in Public Infrastructure
Operational technology networks in government settings were engineered for longevity, not cybersecurity. Many municipal SCADA systems controlling water distribution, wastewater treatment, and traffic signal infrastructure run on hardware and software designed decades before network connectivity became standard. The result is a vast attack surface of legacy devices, flat network architectures, and minimal authentication — all now exposed to internet-connected environments through remote access expansions and IoT integration initiatives.
Unlike IT networks where a breach may compromise data, a successful attack on government OT infrastructure can halt physical services entirely. The CISA Cybersecurity Advisory framework categorizes water, energy, and transportation OT systems as Tier-1 critical infrastructure — recognizing that disruptions directly threaten public health and safety. Municipal cybersecurity teams must treat OT protection as a distinct discipline, not an extension of their existing IT security posture.
Embedded PLCs and RTUs running unsupported firmware cannot receive security patches. Many government water and power systems operate on devices with 15–25 year lifecycles — each one a potential entry point for threat actors targeting public infrastructure security gaps.
Most municipal OT networks lack segmentation between engineering workstations, HMI systems, and field devices. A single phishing compromise of a remote access account can give attackers lateral movement across the entire SCADA environment without encountering a single internal barrier.
COVID-era remote access expansions left many government OT environments with VPN connections lacking multi-factor authentication, vendor remote access accounts that are never deprovisioned, and jump servers with default credentials still in place.
Smart city initiatives have introduced thousands of connected sensors, environmental monitors, and building management devices into municipal OT environments — most provisioned with minimal security configuration and no ongoing visibility into their network behavior.
SCADA Security for Government: Core Protection Requirements
Effective SCADA security for government facilities requires purpose-built controls that account for the operational constraints of public infrastructure — including 24/7 uptime requirements, zero-tolerance for operational disruption during security implementation, and the heterogeneous vendor environments typical of municipal systems. Agencies that book a demo with iFactory typically discover significant visibility gaps in their existing SCADA environments within the first week of passive network monitoring deployment.
OT Asset Discovery and Inventory Management
You cannot secure what you cannot see. Government OT cybersecurity begins with passive asset discovery that identifies every PLC, RTU, HMI, historian, and engineering workstation on the network — including devices that were never formally documented. Continuous asset inventory tracks firmware versions, communication protocols, and network behavior baselines for each device, establishing the foundation for anomaly detection and vulnerability management across municipal SCADA environments.
Network Segmentation and OT/IT Convergence Security
Implementing network segmentation in government OT environments requires a phased approach that preserves operational continuity while isolating critical control zones from corporate IT networks, DMZ environments, and internet-facing systems. NIST SP 800-82 and IEC 62443 both prescribe zone-and-conduit architectures — enforcing strict traffic policies at every OT zone boundary with deep packet inspection capable of parsing industrial protocols including Modbus, DNP3, and BACnet.
Anomaly Detection and OT Threat Monitoring
Signature-based intrusion detection is insufficient in OT environments where known-malicious traffic patterns may not match industrial protocol attack vectors. Behavioral anomaly detection that establishes communication baselines for every device pair — then alerts when a field device initiates an unexpected connection, a new command type appears in a Modbus stream, or an engineering workstation polls a PLC outside its scheduled window — closes the detection gap that conventional IT security tools leave open in SCADA environments.
Privileged Access Management for OT Systems
Every account with engineering workstation access, SCADA historian access, or remote HMI capability represents a potential attack vector. Privileged access management for government OT environments must enforce just-in-time access, session recording, and credential vaulting — with vendor access accounts automatically deprovisioned after session completion, eliminating the persistent third-party access vulnerabilities common in municipal infrastructure networks.
Vulnerability Assessment Without Operational Disruption
Active vulnerability scanning can disrupt or crash legacy OT devices — a non-starter in government water, power, and transportation environments. Passive vulnerability assessment using device fingerprinting, firmware version correlation against public CVE databases, and protocol behavior analysis identifies critical exposures without generating a single packet that could impact field device operations. Agencies can book a demo to review passive assessment methodology applied to their specific OT environment.
IoT Device Protection in Municipal and Smart City Infrastructure
Smart city initiatives have dramatically expanded the IoT attack surface across government networks. Environmental sensors, smart meters, connected streetlights, building management systems, and public safety cameras all introduce network-connected endpoints that share OT network segments with critical control systems — but are rarely managed with the same security discipline. Effective IoT device protection in public infrastructure requires automated onboarding controls, behavioral monitoring, and micro-segmentation policies that contain potential compromises before they spread to SCADA or ICS environments.
Every new IoT device is identified, profiled, and assigned to the correct network segment before it can reach control system infrastructure — enforced automatically without manual intervention.
Behavioral profiles define normal communication for each device type. Deviations — unexpected outbound connections, new protocols, or anomalous data volumes — are flagged as potential compromise or misconfiguration.
Continuous firmware inventory correlated against CVE databases identifies which endpoints carry known critical vulnerabilities — prioritized by network location and potential blast radius in the OT environment.
Micro-segmentation policies enforced at the protocol level block IoT devices from initiating connections to OT control zones — eliminating the pivot path that makes smart city security a critical infrastructure concern.
Vendor devices are network-isolated, vendor remote access is session-limited, and device traffic is monitored independently — closing the supply chain security gap common in municipal IoT deployments.
Automated workflows detect inactive devices, flag end-of-life firmware, and enforce network removal — preventing ghost devices from becoming persistent footholds in municipal infrastructure environments.
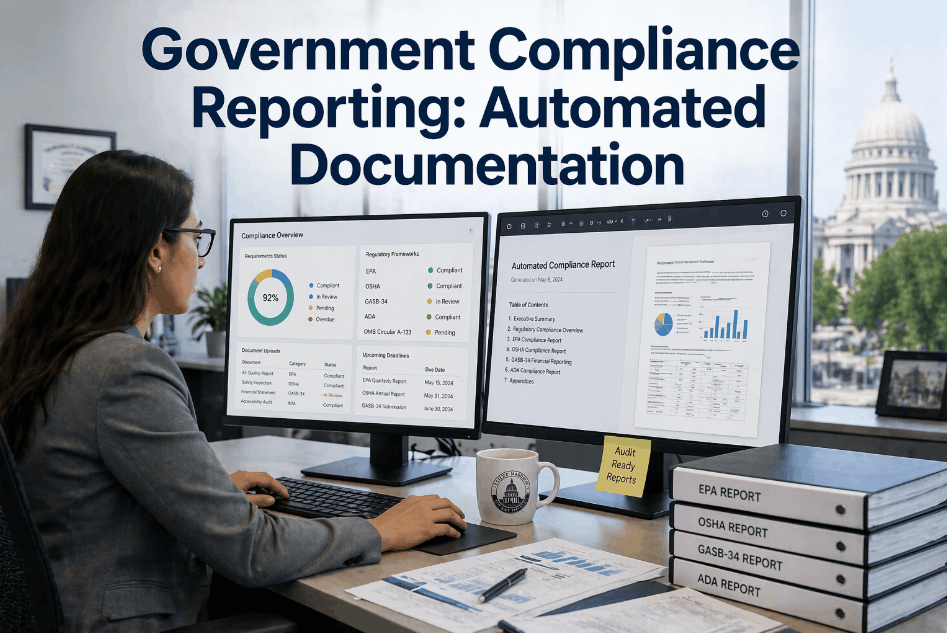
Regulatory Compliance Framework for Government OT Cybersecurity
Government OT security programs must satisfy a layered compliance environment that spans federal requirements, sector-specific mandates, and international standards. Understanding how these frameworks interrelate — and where a single analytics platform can serve all of them — is essential for municipal cybersecurity teams managing limited resources across broad infrastructure portfolios. Agencies can book a demo to see how iFactory maps its OT monitoring outputs directly to NERC CIP, NIST SP 800-82, and IEC 62443 documentation requirements.
| Compliance Framework | Applies To | Key OT Security Requirements | Documentation Mandate | iFactory Coverage |
|---|---|---|---|---|
| NIST SP 800-82 | Federal and municipal ICS/SCADA environments | Asset inventory, network segmentation, access control, incident response | Security architecture documentation, risk assessments | Asset discovery, zone mapping, risk scoring dashboards |
| NERC CIP | Electric utility OT systems (BES Cyber Systems) | Electronic security perimeters, physical security, system security management | Electronic access logs, configuration change records | Access audit trails, configuration baseline tracking |
| IEC 62443 | Industrial automation and SCADA globally | Zone and conduit model, security levels, supply chain security | Security management system records, SL assessments | Zone policy management, SL gap analysis reporting |
| CISA Cybersecurity Framework | All critical infrastructure sectors | Identify, Protect, Detect, Respond, Recover | Cyber risk management documentation, incident records | Risk dashboards, incident workflow, recovery documentation |
| EPA Water Sector Cybersecurity | Municipal water and wastewater systems | Cybersecurity assessment, emergency response plan updates | Risk and resilience assessments, updated ERP records | Automated risk assessments, plan update tracking |
| TSA Security Directives | Pipeline and surface transportation OT | Network segmentation, access control, continuous monitoring | Implementation plans, annual assessments | Segmentation evidence, monitoring reports, assessment records |
Incident Response for Government OT Cyber Attacks: What Municipalities Need Now
When a cyber incident affects government OT infrastructure, the response timeline is measured in minutes — not hours. The 2021 Oldsmar water treatment attack demonstrated that a compromised HMI connection could allow an attacker to modify chemical dosing setpoints in real time. Effective OT incident response for municipal infrastructure requires detection capabilities, playbooks, and isolation procedures that are pre-configured and exercised before an attack occurs — not assembled during one. Security teams looking to validate their response readiness can book a demo to walk through iFactory's incident simulation framework.
Real-Time OT Threat Detection and Alerting
Continuous behavioral monitoring that generates alerts within seconds of detecting anomalous OT network activity — including unauthorized command sequences, unexpected device communications, and protocol violations that indicate active intrusion or insider threat activity in SCADA environments.
Automated OT Network Isolation Procedures
Pre-configured isolation playbooks that allow operators to segment compromised OT zones from the broader network with a single authorized action — maintaining safe operational states in remaining zones while containing an active intrusion to its initial foothold environment.
Forensic Evidence Capture and Audit Trail
Tamper-evident network flow logs, command sequence records, and access audit trails that give government incident response teams and federal investigators the forensic foundation required to determine attack origin, scope, and dwell time in OT environments where log data is often sparse or absent.
Safe State Monitoring During Recovery
Continuous monitoring of OT device states during recovery operations confirms that field devices are operating within safe parameters after an incident — providing the verification evidence required before isolated systems are reconnected to the broader municipal infrastructure network.
CISA and Federal Reporting Integration
Pre-formatted incident reporting templates aligned with CISA reporting requirements and sector-specific notification mandates — reducing the administrative burden on municipal cybersecurity teams during active incident response when attention must remain on operational recovery.
Post-Incident Vulnerability Remediation Tracking
Structured remediation workflows that track every vulnerability identified during an incident investigation through to confirmed closure — generating the corrective action evidence required for compliance reporting to federal oversight bodies and elected oversight stakeholders in government infrastructure environments.
ROI and Operational Impact of Municipal OT Cybersecurity Programs
The business case for government OT cybersecurity investment extends beyond compliance and risk avoidance. Municipalities that implement integrated OT security platforms consistently report operational efficiency gains alongside security improvements — as real-time asset visibility and network monitoring generate operational intelligence that reduces unplanned downtime, accelerates fault diagnosis, and improves infrastructure lifecycle planning. Agencies looking to build this case internally can book a demo and request a ROI analysis customized to their infrastructure portfolio and current security maturity.
Continuous behavioral monitoring closes the detection gap that allows attackers extended dwell time in unmonitored OT environments — limiting the operational impact of any intrusion that does occur.
Automated evidence collection for NERC CIP, NIST SP 800-82, and CISA framework requirements reduces audit preparation from weeks of manual record compilation to targeted report generation.
CISA incident analysis shows that the majority of successful OT attacks exploit known vulnerabilities in assets that were not inventoried — underscoring that visibility is the primary prerequisite for government OT protection.
Government OT breaches carry costs far beyond IT incidents — including emergency service restoration, public health response, and federal investigation support, all of which dwarf the investment required for proactive OT security.
Common Challenges in Government OT Security Programs — and How to Resolve Them
OT and IT Security Team Silos
Municipal OT and IT teams often operate with separate toolsets, separate visibility, and separate incident response procedures. A unified OT security platform with role-appropriate dashboards for both teams — sharing a single asset inventory and alert queue — closes the coordination gap that attackers exploit at the OT/IT boundary.
Budget Constraints in Municipal Cybersecurity
Government OT security investments must be justified to elected bodies and budget committees unfamiliar with operational technology risk. Platforms that quantify existing vulnerabilities, map them to regulatory compliance gaps, and project breach cost avoidance provide the evidence base required to secure OT security funding in municipal budget cycles.
Legacy System Integration Without Disruption
Passive monitoring architectures that capture OT network traffic without communicating with field devices allow security deployment across legacy SCADA environments with zero operational risk — no firmware updates required, no device reboots, no production impact during security onboarding.
Vendor and Contractor Access Management
Municipal infrastructure is maintained by dozens of external vendors whose remote access accounts represent persistent vulnerabilities. Automated vendor access lifecycle management — session-limited credentials, real-time session monitoring, and automatic account deprovisioning — eliminates the most common initial access vector in government OT breaches.
Workforce OT Security Awareness Gaps
OT operators trained on reliability and uptime rather than cybersecurity are more likely to approve social engineering attempts, connect unauthorized devices, or disable security controls that seem to interfere with operational tasks. OT-specific security awareness training integrated with real-world incident data from the facility's own network builds the operational culture that technical controls alone cannot achieve.
Best Practices for Building a Government OT Cybersecurity Program
Start With Comprehensive OT Asset Visibility
Deploy passive network monitoring before any other security control. An accurate, continuously updated asset inventory is the prerequisite for every subsequent security decision — segmentation policy design, vulnerability prioritization, access control scope, and incident response playbook development all depend on knowing what is actually on your OT network.
Implement Network Segmentation in Phases
Apply IEC 62443 zone-and-conduit architecture incrementally — starting with isolation of the highest-consequence systems (water chemical dosing, power grid control, traffic signal management) before expanding segmentation to lower-risk OT zones. Phased segmentation avoids the operational disruptions that cause government agencies to abandon network security projects mid-implementation.
Establish Behavioral Baselines Before Alert Tuning
Allow passive monitoring to observe normal OT network behavior for 30–60 days before configuring anomaly detection thresholds. Behavioral baselines built from actual operational patterns — not generic OT network templates — minimize false positives that cause operations teams to distrust or disable security alerting in municipal infrastructure environments.
Align Security Documentation to Compliance Requirements Early
Configure security platform outputs to generate NERC CIP, NIST SP 800-82, and CISA framework evidence from day one of deployment. Compliance documentation built retroactively from systems not designed to generate it requires manual reconstruction — eliminating most of the audit preparation efficiency that integrated OT security platforms deliver.
Conduct OT-Specific Tabletop Exercises Annually
Cyber incident response exercises in government OT environments must simulate operational scenarios — a compromised water treatment HMI, a ransomware infection spreading from IT to OT, a substation automation failure during peak demand — not generic IT breach scenarios. Annual tabletop exercises using actual platform data validate playbook effectiveness and identify response gaps before real incidents expose them.
Frequently Asked Questions: Government OT Cybersecurity
What is the difference between OT security and IT security in government environments?
IT security protects data and administrative networks. OT security protects physical processes — water treatment, power delivery, traffic management — controlled by SCADA and ICS systems. The key difference is consequence: an OT breach can disrupt essential public services, not just expose data, and standard IT security tools are unsuitable for legacy OT device environments.
What cybersecurity frameworks apply to municipal water and wastewater OT systems?
Municipal water systems must comply with EPA Safe Drinking Water Act cybersecurity requirements, CISA Critical Infrastructure Security guidelines, and NIST SP 800-82. AWIA Section 2013 also requires water systems serving 3,300+ people to conduct cyber risk assessments and maintain updated emergency response plans.
How can government agencies secure legacy SCADA systems that cannot be patched?
Legacy devices must be protected through compensating controls: network segmentation limiting communication to authorized devices only, continuous behavioral monitoring for anomaly detection, application whitelisting on connected engineering workstations, and physical security for devices with no network-level authentication.
What is the typical timeline for deploying OT security monitoring in a municipal environment?
Passive OT monitoring is typically deployed within 6–10 weeks, covering network tap installation, asset discovery, and baseline configuration. Active controls like network segmentation are phased over 3–6 months following initial visibility deployment, depending on network complexity and number of remote sites.
How does iFactory's OT security platform handle environments with both legacy ICS and new IoT devices?
iFactory uses passive monitoring that requires no interaction with field devices — making it compatible with legacy PLCs and RTUs. IoT devices are profiled through the same infrastructure, with behavioral baselines and segmentation policies applied per device category across the full municipal OT environment.
READY TO SECURE YOUR OT INFRASTRUCTURE
From SCADA to Smart City IoT — One Platform, Complete Government OT Security.
iFactory's OT cybersecurity platform delivers continuous asset visibility, behavioral anomaly detection, and compliance-ready documentation for municipal water, power, transportation, and smart city OT environments — with passive deployment that never disrupts the infrastructure it protects.