Every unpatched PLC, every flat OT network, every SCADA terminal exposed to the corporate LAN is a ticking liability — and the average cost of an industrial cyber incident now exceeds $3.1 million per event. Security teams that delay IEC 62443 alignment aren't saving budget; they are accumulating risk that regulators, insurers, and adversaries will eventually price for them. iFactory's Edge AI Deployment layer closes that gap — bringing continuous threat visibility to the network perimeter where legacy tools go blind.
iFactory Edge AI Deployment
SCADA Cybersecurity & IEC 62443 Compliance for Industrial Networks
Network segmentation, real-time threat detection, and automated compliance reporting — purpose-built for OT environments where downtime is not an option.
$3.1M
Avg. industrial cyber incident cost
73%
Of OT attacks exploit flat networks
IEC 62443
Global OT security standard
<60s
Edge AI anomaly detection latency
The Hidden Cost of OT Security Debt
Industrial control systems were engineered for reliability, not adversarial environments. SCADA platforms running Windows XP, PLCs with default credentials, and historian servers bridging IT and OT without segmentation are not legacy curiosities — they are active attack surfaces. Threat actors have noticed: ICS-targeted malware families have tripled since 2020, and critical infrastructure operators now face nation-state-level adversaries alongside opportunistic ransomware groups. IEC 62443 exists precisely to impose structured defense across these environments. Organisations that treat compliance as a checkbox exercise rather than an operational discipline will find that auditors are the least of their problems.
⚠
Regulatory Exposure
NERC CIP violations carry fines up to $1M per day per violation. IEC 62443 non-conformance increasingly triggers insurance exclusions.
🔒
Operational Downtime
A single ransomware event on an unsegmented OT network can halt production for 7–21 days — losses that dwarf any security investment.
📊
Reputational Damage
Public disclosure of an ICS breach triggers supply-chain audits from customers, lenders, and insurers simultaneously.
See how iFactory maps your SCADA topology to IEC 62443 Security Levels in under 48 hours.
Book a Demo
IEC 62443 Explained: What Compliance Actually Requires
IEC 62443 is a multi-part standard published by the International Electrotechnical Commission governing cybersecurity for industrial automation and control systems. It defines four Security Levels (SL 0–4) mapped to consequence severity and mandates countermeasures across seven Foundational Requirements: identification and authentication control, use control, system integrity, data confidentiality, restricted data flow, timely response to events, and resource availability. Compliance is not binary — it is a maturity continuum requiring documented policies, technical controls, and verified monitoring at every layer of the Purdue Model.
Dimension
Legacy Friction — Old Way
Optimised Excellence — iFactory
Network Segmentation
Flat OT/IT network; SCADA visible from corporate LAN
Edge AI enforces zone-and-conduit model; micro-segments PLC subnets automatically
Patch Management
Manual tracking in spreadsheets; 18-month average lag on OT patches
Automated vulnerability scanning; risk-ranked patch queue with change-window scheduling
Threat Detection
IT SIEM blind to OT protocols; Modbus/DNP3 traffic uninspected
Edge AI decodes OT protocols natively; anomaly alerts in under 60 seconds
IEC 62443 Reporting
Manual evidence collection; audit prep takes 6–8 weeks per cycle
Continuous compliance dashboard; audit-ready reports generated on demand
Access Control
Shared credentials on HMIs; no privileged access management
Role-based access with MFA; session logging tied to work-order context
Incident Response
No OT-specific playbooks; IT team unfamiliar with PLC recovery
AI-guided runbooks; automated isolation of compromised zones within seconds
How iFactory Edge AI Closes the OT Security Gap
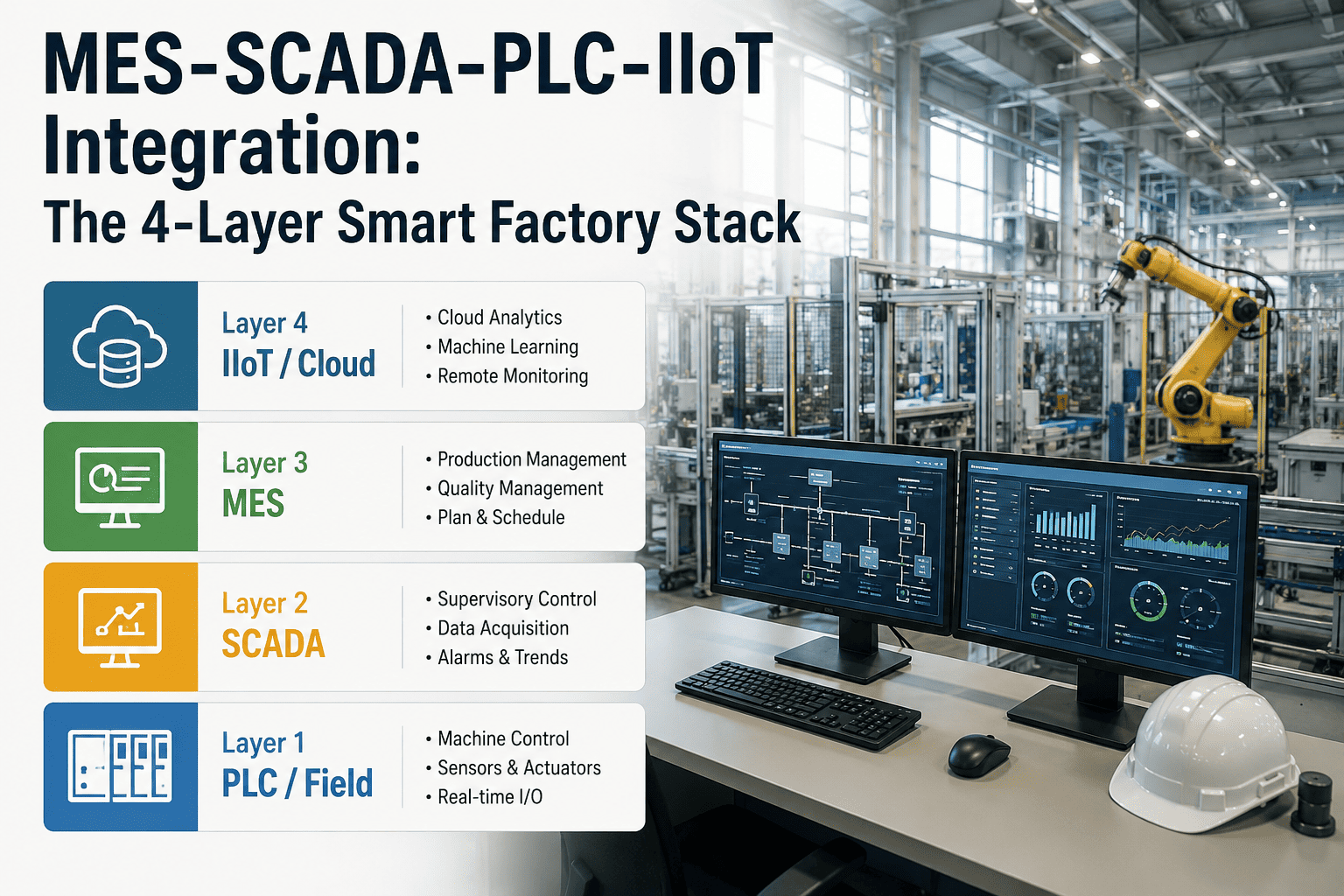
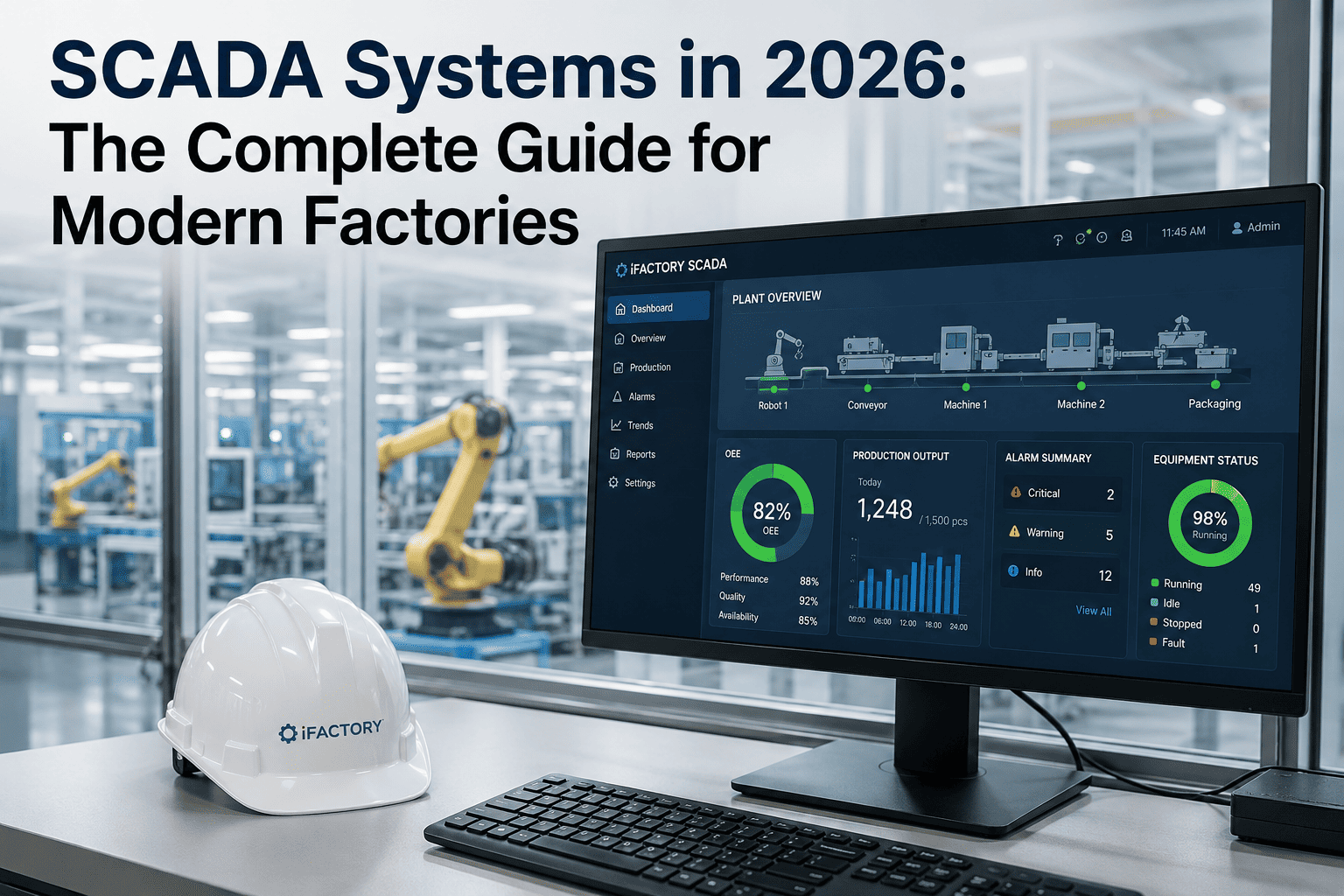
Traditional IT security tools fail in OT environments for a fundamental reason: they were not designed to understand industrial protocols, tolerate high-availability constraints, or operate at the network edge without cloud round-trips. iFactory's Edge AI Deployment layer is purpose-built for SCADA and PLC environments — processing Modbus, DNP3, EtherNet/IP, and PROFINET traffic locally, enforcing IEC 62443 zone boundaries, and feeding the digital twin with continuous security telemetry.
🚫
Zone & Conduit Enforcement
- Automatic Purdue Model zone mapping
- Conduit traffic whitelisting per IEC 62443-3-3
- Lateral movement blocked at switch level
- Air-gap simulation for critical PLCs
🔎
OT-Native Threat Detection
- Deep packet inspection for 15+ OT protocols
- Baseline deviation alerts under 60 seconds
- Command injection and replay attack detection
- MITRE ATT&CK for ICS mapping built in
📋
Continuous Compliance
- IEC 62443 SL gap assessment on demand
- NERC CIP evidence collection automated
- Audit-ready PDF reports in one click
- Remediation roadmap with prioritised actions
Request a live SCADA threat simulation against your network topology — zero disruption to operations.
Book a Strategy Session
The IEC 62443 Implementation Roadmap
Achieving IEC 62443 conformance is a phased engineering discipline, not a one-time audit. iFactory structures compliance delivery across four stages — each with measurable gate criteria so leadership can track progress in financial terms rather than slide decks.
Stage 1Weeks 1–3
Asset Discovery & Risk Baseline
- Passive OT asset inventory — no active scanning
- CVE mapping against discovered firmware versions
- IEC 62443 Security Level gap assessment
- Risk-ranked remediation backlog created
Gate: Full OT asset register with risk scores delivered
Stage 2Weeks 4–8
Segmentation & Access Hardening
- Zone-and-conduit architecture deployed
- Privileged access management for HMIs and historians
- Default credential remediation across PLCs
- Firewall rule audit and OT-specific ACL deployment
Gate: IT/OT traffic isolation verified; zero shared credentials
Stage 3Months 3–5
Continuous Monitoring & Detection
- Edge AI sensors deployed at zone boundaries
- OT SIEM fed with decoded industrial protocol telemetry
- Incident response playbooks tested via tabletop exercise
- Patch management workflow integrated with CMMS
Gate: Mean time to detect anomaly under 5 minutes
Stage 4Month 6+
Audit-Ready Compliance Operations
- IEC 62443 and NERC CIP dashboards live
- Automated evidence packages for external auditors
- Quarterly Security Level re-assessment automated
- Supply-chain vendor risk scoring integrated
Gate: First external audit passed; zero critical findings
Business Impact: Security as a Profit Centre
IEC 62443 compliance is not merely a cost of doing business — it is a competitive differentiator that unlocks lower insurance premiums, preferred vendor status with regulated customers, and reduced unplanned downtime. Organisations that quantify security investment in operational terms consistently achieve faster board approval and faster deployment cycles.
Insurance Premium Reduction
15–30%
Documented OT controls trigger cyber-insurance discounts from most major carriers
Downtime Cost Avoidance
$800K–$4M/yr
Based on one prevented ransomware event per year at typical process-plant downtime rates
Audit Cost Reduction
60–70%
Automated evidence collection eliminates manual prep that averages 6–8 weeks of engineering time
NERC CIP Fine Avoidance
Up to $1M/day
Continuous compliance monitoring eliminates the gap between audit cycles where violations accumulate
Frequently Asked Questions
Does deploying Edge AI sensors require a plant shutdown?
No. iFactory's passive monitoring architecture uses span ports and network taps to capture OT traffic without injecting packets into the control network. Installation is non-intrusive and does not require PLC configuration changes. Most deployments are completed within a scheduled maintenance window of 4–8 hours.
Which IEC 62443 Security Levels does iFactory support?
iFactory's platform maps technical controls to SL 1 through SL 3 requirements. SL 4 — designed for nation-state threat resistance — involves physical and procedural controls beyond software scope, though iFactory's telemetry feeds directly into SL 4 assessment frameworks used by certified ISA/IEC 62443 assessors.
How does iFactory handle air-gapped OT networks?
Edge AI processing occurs entirely on-premises. No OT telemetry leaves the facility. Compliance reports and dashboards synchronise via a one-way data diode to the corporate network. Environments with strict air-gap requirements can operate iFactory in fully offline mode with scheduled report exports.
Can iFactory integrate with our existing IT SIEM?
Yes. iFactory translates decoded OT protocol events into normalised CEF and LEEF formats compatible with Splunk, Microsoft Sentinel, IBM QRadar, and most major SIEM platforms. This gives IT security teams visibility into OT anomalies without requiring OT protocol expertise.
Start Secure. Stay Compliant. Scale Confidently.
Your IEC 62443 Compliance Journey Begins with a Free OT Security Assessment
iFactory's Edge AI Deployment team maps your SCADA topology, identifies your highest-risk exposure points, and delivers a prioritised IEC 62443 remediation roadmap — at no cost and with zero disruption to operations.
48hr
OT asset discovery turnaround
Zero
Production disruption during deployment
SL 1–3
IEC 62443 Security Levels covered
10-30x
Return on security investment