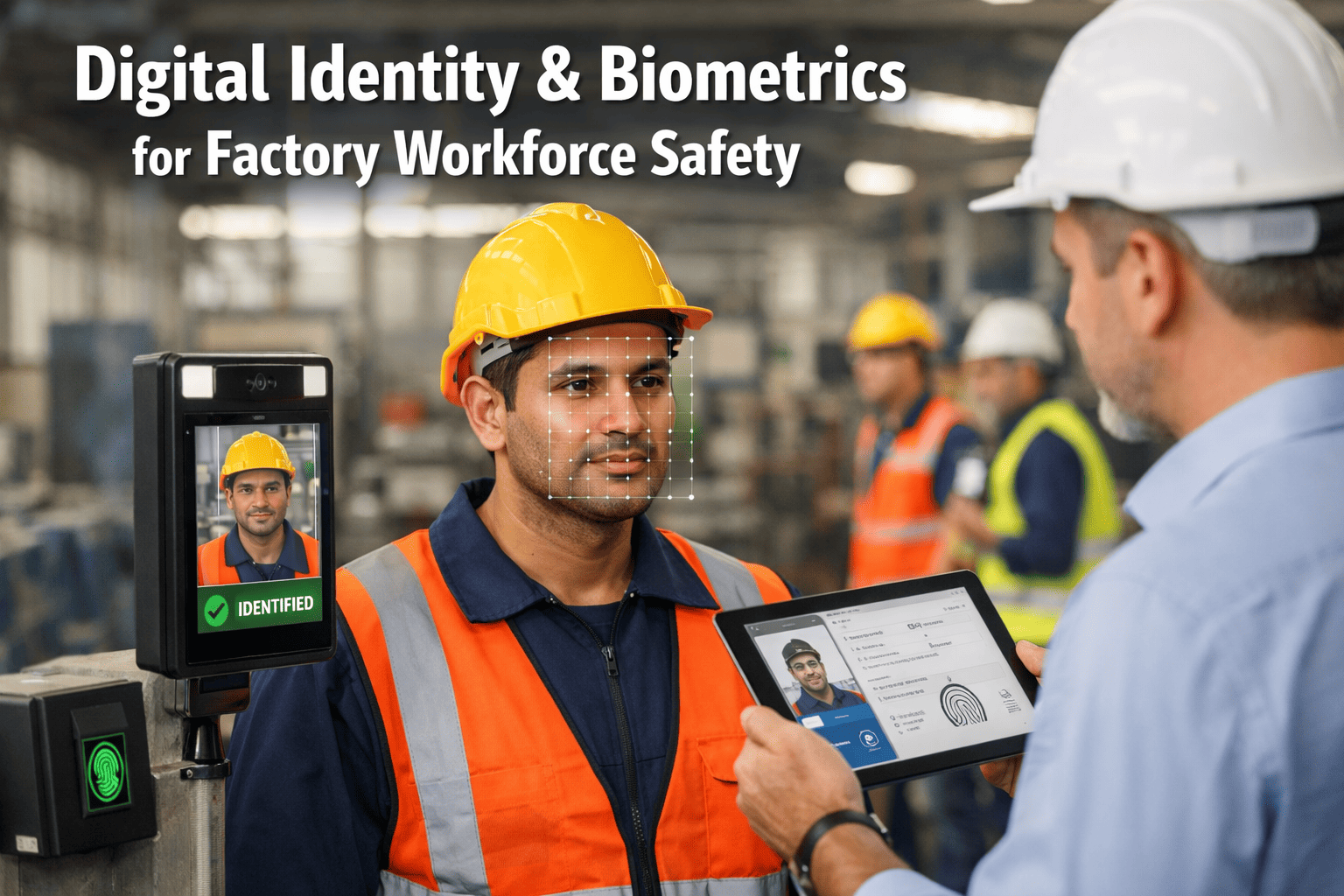
When a manufacturing worker's biometric data is compromised, it doesn't just cost a password reset — it costs an irreversible breach of personal identity. Unlike a stolen credential, a compromised fingerprint or facial scan cannot be revoked, replaced, or rotated. That single reality is why 78% of industrial safety directors, when surveyed in 2024, said biometric data sovereignty was either their current requirement or their top planned investment for 2025. The manufacturing sector holds some of the most sensitive workforce data in industry: biometric enrollment templates, behavioral gait analysis, health vitals from wearables, and access patterns that reveal worker movements throughout facilities. Sending that data to a shared cloud environment is a risk a growing number of safety managers are no longer willing to accept.
On-Premise Digital Identity & Biometrics for Factory Workforce Safety
A complete guide to deploying biometric identity and safety systems where your most sensitive workforce data belongs — inside your own walls, under your own control, with zero external exposure.
The Biometric Data Manufacturers Cannot Afford to Expose
Before examining the technology, it's worth being precise about what on-premise biometric systems are protecting. Manufacturing facilities hold multiple categories of workforce data that carry extraordinary personal privacy and safety sensitivity.
Biometric Enrollment Templates
Mathematical representations of fingerprints, facial geometry, iris patterns, and vein structures that serve as irreversible digital identities. Unlike passwords, these cannot be changed if compromised — making their protection paramount under GDPR Article 9 and similar biometric privacy laws.
Behavioral Biometrics
Gait analysis, typing cadence, and movement patterns used for continuous authentication and fatigue detection. These patterns reveal physical health conditions and personal habits that workers have a legal right to keep private from third-party vendors.
Wearable Safety Vitals
Heart rate variability, body temperature, and stress indicators from industrial wearables. This health data triggers safety interventions but also reveals medical conditions protected under HIPAA and occupational health privacy regulations.
Access Pattern Intelligence
Time-stamped entry/exit logs, zone traversal patterns, and workstation associations that reconstruct a worker's complete facility movements. This data reveals shift schedules, break patterns, and workstation assignments that could enable stalking or targeted theft.
Incident Response Biometrics
Biometric verification logs during safety incidents, evacuation mustering, and emergency access events. These timestamps prove compliance with evacuation protocols but also document worker locations during traumatic events, requiring strict confidentiality.
Third-Party Contractor Data
Biometric profiles of temporary workers, maintenance contractors, and visitors who lack full-time employee protections. This data often lacks clear ownership boundaries, creating liability gaps when stored in external cloud environments.
Why Cloud-First Biometric Systems Create Structural Risk for Manufacturing
Cloud identity platforms offer genuine capabilities, but their architecture creates exposure points that are difficult to fully mitigate in industrial safety environments.
Irreversible Data Exposure
Biometric templates, once transmitted to cloud servers, exist outside organizational control permanently. Even if the contract terminates, copies may persist in backup systems, disaster recovery sites, or subcontractor infrastructure — creating a lifetime identity theft risk for workers.
Cross-Border Data Transfer
Cloud providers route biometric data through global server networks for load balancing. Manufacturing facilities operating under GDPR, China's PIPL, or Illinois BIPA face automatic compliance violations when worker biometrics traverse jurisdictions with inadequate privacy protections.
Vendor Lock-in Risks
Cloud biometric platforms use proprietary template formats that cannot be exported or migrated. When a manufacturer switches providers, workers must re-enroll their biometrics — a process that disrupts operations and creates temporary security gaps during transition periods.
Latency-Critical Safety Failures
Cloud-based biometric verification requires network round-trips that introduce 200-500ms delays. For safety-critical access control — such as emergency lockdown overrides or hazardous area entry — this latency creates unacceptable risks during time-sensitive evacuations or equipment failures.
Deploy iFactory On-Premise and Keep Workforce Biometrics Inside Your Facility
iFactory's on-premise biometric deployment gives manufacturers full digital identity capability with zero external data exposure — your workers' templates, your access logs, your safety infrastructure.
Protect fingerprint, facial recognition, and behavioral biometrics by running all identity verification and safety analytics entirely within your facility network. No third-party cloud access. No cross-border transfer risk. Full compliance with GDPR Article 9, Illinois BIPA, and OSHA requirements — all from a single on-premise platform built for industrial workforce safety.
On-Premise Biometric Architecture: Four Deployment Models for Workforce Safety
Not all on-premise biometric deployments are equivalent. Manufacturing facilities can choose from four distinct architectural approaches based on their security requirements, existing access control infrastructure, and operational complexity tolerance.
Fully Air-Gapped Biometric Vault
Biometric enrollment and verification servers are physically isolated from all external networks. Template storage occurs on encrypted local hardware security modules (HSMs) with no network interfaces. Ideal for defense contractors, critical infrastructure, and facilities under national security frameworks where biometric data exfiltration must be physically impossible.
Private On-Premise with Secure Update Channel
Biometric infrastructure operates entirely on-site with controlled, scheduled outbound connections for algorithm updates and threat intelligence only. No biometric templates or access logs ever leave the facility. This model balances strong privacy protection with the operational benefit of receiving anti-spoofing algorithm improvements without manual intervention. Book a demo to see this deployment configuration for your workforce.
On-Premise Core with Anonymized Safety Analytics
Sensitive biometric templates and individual access logs remain on-premise. Aggregated, anonymized safety metrics — incident response times, zone occupancy rates, evacuation flow patterns — are shared with a corporate analytics layer for safety optimization. A strictly defined data governance policy determines exactly which data elements may traverse the boundary, with all individual identifiers stripped.
Edge Biometric Inference
Biometric matching algorithms run directly on edge devices at access points — turnstiles, door readers, and workstation terminals. Templates are distributed as encrypted inference models to each edge node. No centralized biometric database exists; each device verifies identity locally against its encrypted template store. Schedule a consultation to see how iFactory supports edge biometric deployments for high-throughput manufacturing environments.
Regulatory Frameworks That Drive On-Premise Biometric Adoption
For many manufacturers, on-premise biometric systems aren't a preference — they're a compliance requirement. Understanding which frameworks apply to your workforce is foundational to biometric infrastructure planning.
The Evolution of Industrial Biometric Safety
Understanding the chronological development of biometric technology in manufacturing reveals why on-premise deployment has become the preferred architecture for workforce safety.
Physical Key & PIN Era
Manufacturing access control relied on mechanical keys and shared PINs. No biometric data existed, but security was low and audit trails were non-existent. Lost keys required expensive rekeying; shared PINs created accountability gaps.
Early Biometric Adoption
First fingerprint scanners deployed in high-security manufacturing zones. Standalone devices stored templates locally with no network connectivity. Limited to single-door access with no central management.
Cloud Biometric Platforms Emerge
Biometric-as-a-Service models promised centralized management across multiple facilities. However, this concentrated sensitive template data in third-party servers, creating the sovereignty and compliance risks we face today.
GDPR and BIPA Enforcement
Landmark fines against companies for improper biometric data handling ($1.2B under GDPR, $650M under BIPA). Manufacturing legal teams began mandating on-premise biometric storage to eliminate third-party liability.
Edge AI Biometric Processing
On-device neural networks enabled biometric matching without centralized databases. Manufacturing facilities could deploy high-speed facial recognition with templates distributed across edge devices, eliminating single points of failure.
On-Premise Biometric Sovereignty Standard
78% of industrial safety directors now require on-premise biometric architectures. Air-gapped enrollment, edge inference, and zero-knowledge templates have become baseline requirements for workforce safety systems.
On-Premise vs. Cloud Biometric Architecture Comparison
A visual comparison of data flow and exposure points between cloud-dependent and on-premise biometric systems for manufacturing workforce safety.
High-Risk Data Exposure
Zero External Exposure
How iFactory Delivers On-Premise Biometric Identity for Workforce Safety
iFactory is engineered from the ground up to support on-premise biometric deployment for manufacturers who cannot — or will not — route sensitive workforce identity data through external cloud infrastructure. The platform provides full biometric capability within a deployment architecture you control entirely. Book a demo to see the on-premise biometric deployment in action.
The platform covers fingerprint and facial recognition access control, behavioral biometrics for fatigue detection, wearable integration for safety vitals, and automated mustering during emergencies — all running within your facility's network perimeter. Template updates and anti-spoofing algorithm improvements are delivered through controlled, cryptographically signed packages that your IT team reviews before deployment.
For manufacturers with multiple facilities, iFactory supports a federated identity architecture where each site maintains its own encrypted biometric vault while enabling cross-site access for authorized personnel. Critically, biometric templates remain siloed at each facility — no central biometric database is created, eliminating the high-value target that attracts sophisticated attackers. Schedule a safety consultation to discuss multi-site biometric deployment strategies.
Quantifying the Impact: On-Premise Biometric Safety Outcomes
Data from manufacturing facilities that have transitioned from cloud-based to on-premise biometric systems reveals measurable improvements in security, compliance, and operational efficiency.
Ready to Secure Your Workforce Biometric Data On-Premise?
Speak with an iFactory biometric specialist about on-premise deployment options tailored to your facility's safety and privacy requirements.
Whether you need a fully air-gapped biometric vault, a private on-premise deployment with secure update channels, or a federated edge inference model — iFactory adapts to the privacy architecture your workforce deserves. Keep your employees' fingerprints, facial geometry, and safety biometrics permanently inside your own walls while gaining the full power of AI-driven access control and emergency mustering.
Frequently Asked Questions
What happens to biometric data if we terminate our iFactory contract?
Because iFactory operates on-premise, you maintain full control of your biometric database at all times. Upon contract termination, you retain encrypted template files that can be migrated to alternative systems using standard data export protocols. Unlike cloud biometric services, there is no "deletion" process — you simply discontinue software updates while preserving your data sovereignty. We provide 90 days of transition support to ensure seamless migration to your next platform.
How does on-premise biometric verification handle emergency evacuations?
On-premise edge biometric devices continue functioning during network outages, internet failures, or cloud service disruptions — precisely when emergencies are most likely to occur. Each access point maintains local template storage and battery backup power. Emergency mustering stations can verify worker identity against local databases even during facility-wide power failures using uninterruptible power supplies. This resilience is impossible with cloud-dependent systems that fail when connectivity is compromised.
Can workers refuse biometric enrollment under on-premise systems?
Yes. iFactory's on-premise architecture supports multiple authentication modalities — biometrics, smart cards, and PINs — allowing facilities to accommodate workers with religious objections, medical contraindications, or privacy concerns. For workers who do enroll, GDPR Article 9 requires explicit consent, which iFactory documents through digital consent workflows with audit trails. Workers retain the right to withdraw consent and request template deletion at any time, with iFactory's local data architecture enabling immediate compliance.
How do on-premise systems prevent biometric spoofing attacks?
iFactory deploys ISO/IEC 30107-3 compliant presentation attack detection (PAD) algorithms directly on each biometric capture device. Liveness detection uses multispectral imaging to distinguish live tissue from printed photos, silicone molds, or replayed video. Because these algorithms run locally on edge devices, they cannot be bypassed by network attacks on central servers. Regular algorithm updates are delivered through signed packages that your security team reviews before deployment.
What hardware is required for on-premise biometric deployment?
A typical manufacturing facility requires: (1) Encrypted biometric enrollment stations with hardware security modules for template generation; (2) Edge biometric readers at access points with local template storage and anti-spoofing sensors; (3) A local authentication server for cross-device synchronization and audit logging. For a 500-worker facility, this typically comprises 2 enrollment stations, 15-20 access readers, and a single rack-mounted server. iFactory conducts site assessments to specify exact hardware requirements based on your access point topology and throughput needs.
How does iFactory handle biometric data for temporary contractors?
iFactory's on-premise architecture enables strict data segregation between employee and contractor biometric templates. Contractor data can be stored on separate encrypted partitions with automatic deletion triggers upon contract expiration — typically 30 days after last access. This prevents the "data creep" common in cloud systems where temporary worker biometrics accumulate indefinitely. Facilities maintain full audit trails of contractor template creation and deletion for compliance with BIPA retention requirements.