Protecting food manufacturing lines from cyber threats has evolved from a secondary IT concern into a critical operational necessity. In an era of connected production, manufacturers who prioritize OT security and industrial network protection gain a significant advantage: reduced risk of ransomware-induced downtime, secured intellectual property, and a robust defense against supply chain disruptions. For facilities still relying on outdated legacy systems without active monitoring, the gap between their vulnerability and the sophistication of modern cyber-attacks grows every day. If your facility is evaluating its next step toward digital resilience, Book a Demo to see how a purpose-built industrial cybersecurity platform can safeguard your production environment from the floor up.
What Is Food Manufacturing Cybersecurity and Why Production Continuity Depends on It
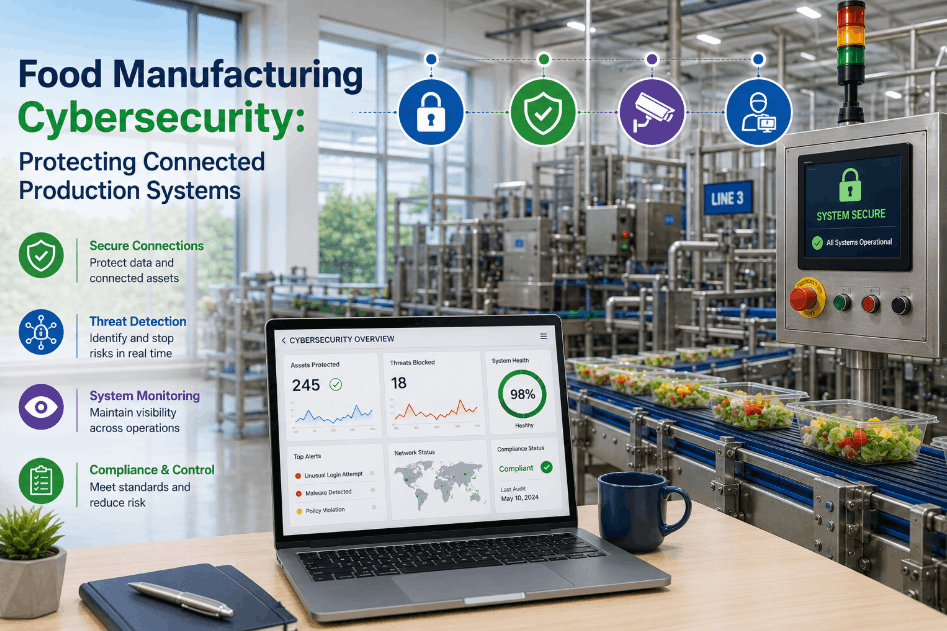
Food manufacturing cybersecurity refers to the specialized tools and protocols used to protect Operational Technology (OT) and industrial control systems from digital interference. Unlike standard office security, industrial cybersecurity for food processing focuses on maintaining the integrity of high-speed production lines, ensuring that PLCs, SCADA systems, and industrial IoT sensors remain operational and uncompromised by ransomware or unauthorized configuration changes. As plants become more automated, the reliance on these systems makes them prime targets for sophisticated threat actors looking to disrupt global supply chains.
The financial impact of a breach is staggering. A single ransomware event can halt a mid-sized facility for days, resulting in millions of dollars in lost production, spoilage of perishable goods, and long-term brand damage. Furthermore, IoT security in food plants is critical because compromised sensors can lead to food safety risks by altering temperature or mixing parameters without triggering traditional mechanical alarms. This "silent" manipulation of recipes or pasteurization cycles represents one of the most significant risks to modern food safety standards. Cybersecurity management converts these digital risks into manageable engineering controls, providing a safety net for the entire manufacturing process.
When your operations and IT teams are ready to close this reliability gap and secure your facility's future, Book a Demo and benchmark your current facility against these advanced performance and security standards. Implementing a robust security layer not only protects your assets but also provides the data integrity needed for accurate OEE tracking and predictive maintenance modeling.
OT Network Visibility
Industrial cybersecurity provides a live, continuous view of every asset on the production network—eliminating the blind spots that allow malware to dwell and spread undetected across heterogeneous hardware environments.
Impact: Rapid threat isolationPLC Integrity Monitoring
Continuous logic monitoring detects unauthorized changes to machine controllers—preventing malicious interference with production recipes, safety protocols, or equipment duty cycles.
Impact: Secured process integritySecure Remote Access
Zero-trust remote access eliminates the risk of VPN vulnerabilities, allowing vendors and maintenance teams to support equipment without exposing the entire facility network to external risks.
Impact: Controlled third-party riskData Encryption
End-to-end encryption for production telemetry protects sensitive OEE and recipe data from interception as it moves from the edge to the manufacturing intelligence layer, ensuring IP protection.
Impact: Protected Trade SecretsFrom Legacy Vulnerability to Digital Resilience: Three Stages of OT Security Maturity
Transitioning a food processing plant from a flat unmanaged network to a cyber-resilient environment is a structured architectural evolution. Most facilities progress through three levels of maturity as they implement connected food plant security protocols. Identifying your current stage is essential for prioritizing security investments and avoiding common pitfalls associated with over-connectivity without adequate protection layers.
Unmanaged Connectivity
Legacy machines and new IoT devices are connected to a single flat network with no segmentation. A breach anywhere on the network can propagate instantly to every asset, including primary processing lines.
Security Score: Critical RiskPerimeter Defense
A firewall separates IT and OT, but internal traffic remains unmonitored. This "hard shell, soft center" approach fails once an attacker gains access to a single internal endpoint or an authorized vendor laptop.
Security Score: Moderate VulnerabilityCyber-Resilient Factory
Micro-segmentation, zero-trust access, and AI-driven anomaly detection are deployed. Threats are automatically isolated at the edge, ensuring production continuity even during active security events.
Security Score: Maximum ProtectionThe jump from Stage 2 to Stage 3 is where iFactory's manufacturing execution system security layer delivers its greatest value. By integrating deep packet inspection and PLC logic verification directly into the data pipeline, plant directors gain the ability to intercept threats before they reach the physical controller level. This proactive stance is the only way to stay ahead of automated malware that can traverse unsegmented networks in seconds. You can explore how this applies to your specific network architecture when you Book a Demo with our specialized industrial security team.
The Metrics of Cyber Resilience: Quantifying Security ROI and Facility Uptime
Investing in food plant cyber security is no longer just a defensive expense—it is a strategic investment in long-term uptime and brand equity. By applying industrial IoT monitoring to security traffic, manufacturers can measure their Mean Time to Detect (MTTD) and Mean Time to Remediate (MTTR), directly correlating security performance with production reliability. These metrics provide the boardroom-level visibility needed to justify continued modernization of the plant's digital infrastructure.
KPIs That Define a Secure Food Manufacturing Environment
A data-driven security program identifies vulnerabilities before they become production incidents. The following metrics are the benchmarks of a mature OT security framework, significantly improved through automated monitoring, role-based access controls, and AI-driven anomaly detection engines that learn the facility's unique communication patterns.
| Cyber Resilience KPI | Without Active OT Monitoring | With AI-Driven Protection | Risk Reduction Potential |
|---|---|---|---|
| Mean Time to Detect (MTTD) | 180–220 days (industry avg) | < 2 hours (real-time detection) | 99.9% faster detection |
| Unauthorized Access Attempts | Largely unrecorded; undetected | 100% visibility & instant alerts | Zero-blind-spot visibility |
| Ransomware Containment Time | Manual; hours to days | Automated; sub-millisecond | Prevents facility-wide lockout |
| PLC Logic Integrity | Manual verification (monthly) | Continuous AI verification | 100% process assurance |
| Compliance Audit Readiness | Weeks of manual preparation | Continuous; audit-ready dashboards | -90% reporting burden |
| Third-Party Access Control | Unrestricted VPN or shared PW | Zero-Trust / MFA per session | Eliminates vendor entry risk |
The Security Stack: Multi-Layered Protection for the Connected Smart Factory
Building a secure analytics infrastructure does not require a full network replacement or a massive capital expenditure. iFactory's operational technology security architecture layers intelligence on top of existing assets—including legacy PLCs, aging SCADA nodes, and modern IoT sensors—creating a unified security fabric that protects data as it moves from the machine sensor to the boardroom dashboard without introducing latency.
Edge-Level Encryption
Secure IoT gateways encrypt data at the source—ensuring that production metrics and sensitive recipe parameters are unreadable to unauthorized actors on the local network or external intruders.
Micro-Segmentation
Network zoning isolates critical processing lines from the rest of the facility—preventing an infected HMI from spreading malware to upstream pasteurizers or downstream bottling lines.
Anomaly Detection
AI models baseline normal network traffic and PLC communication patterns—flagging even the smallest deviation as a potential reconnaissance event or zero-day breach attempt.
Zero-Trust Remote Access
Eliminates broad VPN access in favor of session-based, role-restricted connectivity for vendors—ensuring that remote equipment support doesn't introduce facility-wide risk.
Integrity Monitoring
Continuous hashing of PLC firmware and logic files detects unauthorized modifications instantly—protecting the physical safety and quality of the production process from tampering.
Compliance Reporting
Automated logs of all OT network changes and access events simplify ISO 27001 and regulatory audits—reducing the administrative cost of maintaining security compliance.
The Financial Case for Security: Reducing the Hidden Cost of Industrial Cyber Risk
Beyond the headline-grabbing ransomware attacks, food manufacturers face micro-disruptions caused by poorly secured IoT networks—including IP theft of proprietary recipes, unauthorized speed adjustments on lines, and data leakage from CMMS data protection layers. These "quiet" risks can degrade facility performance over months without ever triggering a major alarm. A dedicated security-first analytics platform surfaces these silent threats, quantifying their impact on TCO and ranking mitigation priorities by financial risk. Facilities that have secured their networks typically find that booking a demo was the single most important step in protecting their multi-million dollar capital investments and ensuring long-term operational viability.
Furthermore, the integration of security with production analytics allows for better correlation between mechanical failures and digital anomalies. For example, a sudden increase in motor temperature could be a mechanical issue, or it could be a malicious override of the cooling system. Only a unified platform can distinguish between the two, providing the root-cause clarity needed for effective maintenance intervention.
The Six Major Cyber Threats Industrial Security Resolves
The industrial security framework targets specific vulnerabilities that traditional IT firewalls miss. Understanding how these threats impact Availability, Performance, and Quality in your facility is the starting point for any intelligent cybersecurity program. Each of these risks represents a potential point of failure that can be mitigated through proactive monitoring.
Ransomware Lockout
The highest financial risk. Active monitoring detects encryption attempts at the edge, isolating the attack before it spreads to the production schedule and halts the entire plant.
Denial of Service (DoS)
Network floods can crash legacy PLCs and HMIs. Intelligent traffic shaping ensures that critical control data always has priority over non-essential traffic or malicious floods.
Malicious Speed Throttling
Unauthorized changes to inverter setpoints can silently reduce OEE. Integrity monitoring flags any change not tied to a verified production order or maintenance task.
Resource Exhaustion
Compromised IoT sensors used as bots can degrade network performance, causing lag in real-time OEE dashboards and critical analytics feeds needed for decision making.
Recipe Manipulation
The most dangerous quality risk. AI logic verification ensures that batch parameters—temperatures, mix ratios—cannot be altered without verified authorized digital signatures.
Data Integrity Drift
Man-in-the-middle attacks can spoof sensor readings, leading operators to make incorrect adjustments that result in batch-level failures, rework, and wasted raw materials.
Quantifying the ROI of Industrial Cybersecurity: A Compounding Value Model
The financial case for manufacturing intelligence software with integrated security is built on preventing catastrophic loss while optimizing daily operations through data integrity. Unlike pure security software, iFactory's platform becomes more valuable over time as its AI models refine their ability to distinguish between normal process variation and emerging cyber-anomalies. Facilities that Book a Demo consistently report that the security layer pays for itself by preventing just one localized network disruption that would have otherwise cascaded into a plant-wide shutdown.
Immediate: Breach Containment
Automated isolation of a single infected workstation or HMI prevents a facility-wide lockout. For high-volume manufacturers, avoiding a 24-hour lockout frequently exceeds the annual platform cost in one event.
Timeline: Instant ProtectionIntermediate: Insurance & Compliance
Demonstrating active OT monitoring and micro-segmentation allows facilities to qualify for lower cyber insurance premiums and higher coverage limits, while simultaneously reducing the cost of manual audits.
Timeline: 3–6 MonthsLong-Term: Supply Chain Continuity
Securing the supply chain against digital disruption protects critical contracts with major retailers who increasingly require proof of cybersecurity maturity as a condition of their supplier agreements.
Timeline: 6–18 MonthsReduction in lateral threat movement across the production floor through automated micro-segmentation.
Average time to detect unauthorized PLC logic changes or network reconnaissance activity.
Average reduction in cyber insurance premiums for facilities with verified OT monitoring and zero-trust access.
Reduction in labor hours required for security audits and regulatory compliance reporting across multiple standards.
Deploying Cyber-Resilience: A Three-Pillar Industrial Security Framework
Achieving full production line security is a continuous evolution, not a single hardware installation. iFactory follows a phased sequence that delivers immediate protection while building toward a fully autonomous security architecture. This roadmap ensures that each phase is self-funding through risk reduction and operational efficiency gains. To receive a facility-specific security roadmap, Book a Demo with our reliability and security engineering team today.
Asset Inventory & Network Mapping
Establish full visibility of every IP-connected asset on the production floor. This baseline eliminates the shadow IoT devices that serve as entry points for attackers and creates the foundation for all downstream segmentation and monitoring policies.
Phase Duration: 1–2 WeeksActive Monitoring & Access Control
Deploy AI-driven anomaly detection and transition from broad VPNs to zero-trust remote access. This phase ensures that every data flow and user session is verified, encrypted, and logged for security auditing in real-time without impacting line speed.
Phase Duration: 3–6 WeeksAutonomous Defense & Response
Integrate security events with production scheduling and maintenance workflows. At this level, the platform automatically isolates threats, validates machine health after updates, and optimizes performance without security compromises.
Phase Duration: OngoingIndustrial Cybersecurity for Food Production — FAQs
Why can't our existing IT firewall protect the production line?
Standard IT firewalls don't understand industrial protocols like Modbus, EtherNet/IP, or Profinet. They can't see inside the machine communication to detect unauthorized PLC logic changes. Industrial cybersecurity uses deep packet inspection (DPI) to monitor the actual control commands being sent to the machinery, ensuring they match the production plan.
Does network segmentation interfere with real-time OEE data collection?
No. Modern segmentation uses conduits that allow authorized data flows to pass through while blocking everything else. iFactory's platform is designed to maintain high-frequency data polling for analytics while ensuring that those connections cannot be used as attack vectors for lateral movement or data exfiltration.
How do we secure legacy equipment that doesn't support modern security protocols?
Legacy assets are protected using virtual patching and secure edge gateways. By wrapping legacy equipment in a secure network segment, we can monitor its traffic and block exploits at the gateway level—extending the secure life of the asset without requiring expensive and disruptive hardware upgrades.
How does industrial cybersecurity impact FSMA and food safety compliance?
Cybersecurity is now a critical component of FSMA's preventive controls. A breach that alters processing temperatures or cleaning cycles can lead to unsafe products. By securing these controls, our platform provides the documentation and data integrity needed to prove that food safety parameters were never compromised by external or internal digital interference.
What is the role of AI in detecting threats in a food plant environment?
AI models learn the unique rhythm of your production environment—shift changes, sanitation cycles, and product turnovers. This allows the system to distinguish between a normal process change and a malicious anomaly, such as a PLC being programmed at 2 AM on a Sunday, providing much higher accuracy than simple threshold-based alerts.
How do we handle security updates without interrupting 24/7 production?
We use a high-availability architecture and virtual patching that allows for security enhancements at the network layer without requiring a reboot of the actual production equipment. This ensures that your facility stays protected against the latest threats without ever missing a production window or scheduled shipment.
What is the risk of doing nothing in the current threat landscape?
The risk is a total facility lockout or, worse, a silent quality compromise. As food manufacturers become more connected to supply chain partners and cloud analytics, the probability of an accidental breach via a vendor or a phishing link on the corporate network increases every month. Passive vulnerability is the leading cause of unplanned downtime in 2024.