The IoT platform market for infrastructure asset management has fragmented rapidly — and for civil infrastructure owners evaluating their options in 2025, the sheer number of vendors making broadly similar promises makes platform selection one of the most consequential and least straightforward procurement decisions in the digitalisation journey. Choosing the wrong platform means inheriting years of vendor lock-in, integration debt, and data quality problems that undermine the predictive analytics ROI the investment was supposed to deliver. Selecting the right IoT platform for infrastructure asset management requires a structured evaluation framework — one that goes beyond feature checklists and benchmark demos to assess the platform's real-world scalability with heterogeneous sensor estates, its integration architecture with existing GIS and CMMS systems, its data security posture, and the total cost of ownership over the asset management lifecycle. This guide provides that framework. If you want to see how iFactory's infrastructure AI platform is designed around these selection criteria — with deployment evidence from civil infrastructure programmes covering bridges, water networks, tunnels, and energy assets — schedule a platform evaluation session with our infrastructure team.
Evaluating IoT Platforms for Your Infrastructure Portfolio? Start With the Right Framework.
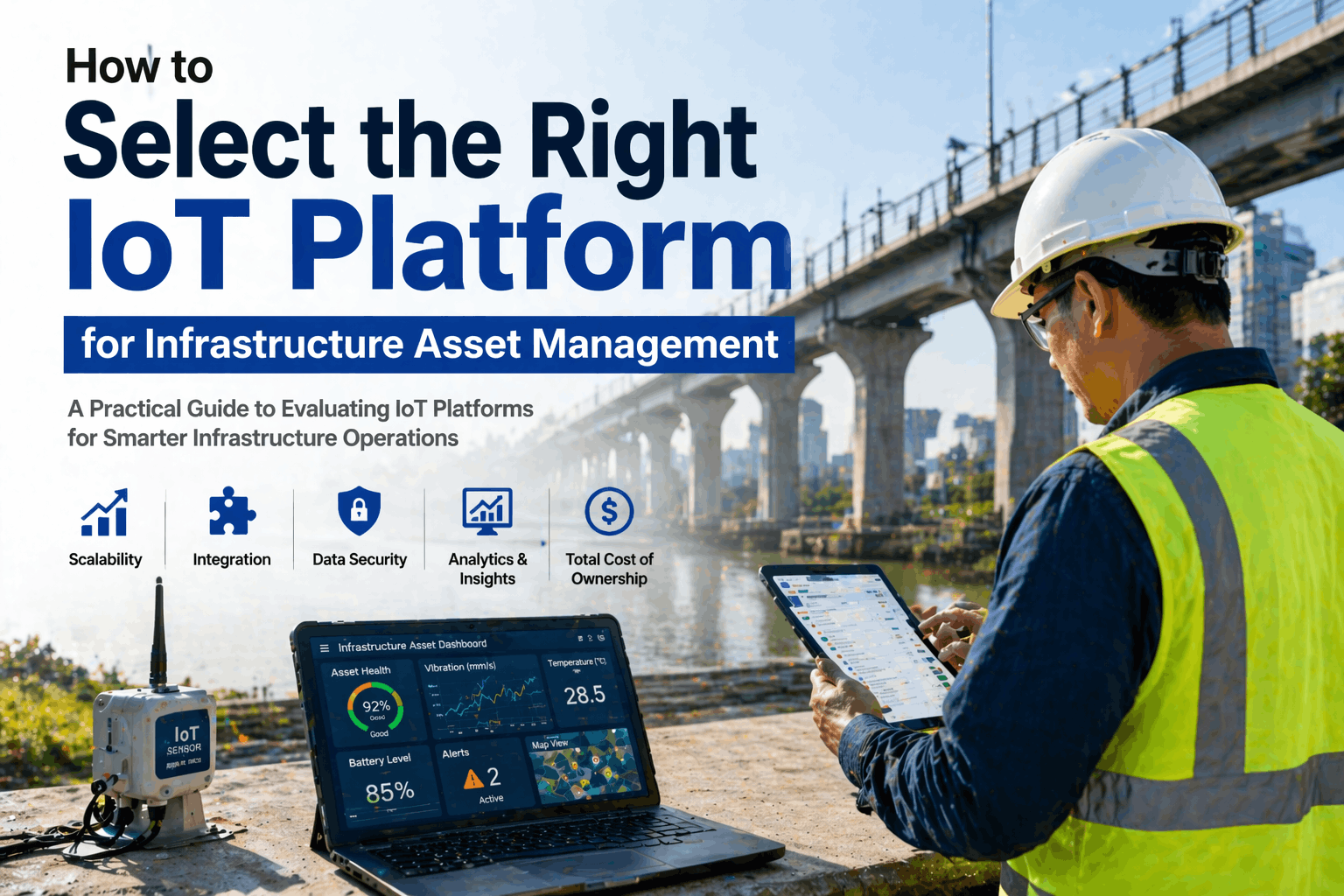
iFactory's infrastructure AI platform is built for the complexity of civil asset management — multi-protocol sensor ingestion, GIS-native asset mapping, CMMS integration, and regulatory compliance documentation — all on a scalable, secure cloud architecture.
Why IoT Platform Selection Goes Wrong in Infrastructure Programmes
Most IoT platform selection processes for infrastructure asset management programmes fail for one of four reasons: they evaluate platforms on demo-environment performance rather than real-world sensor estate complexity; they underweight integration requirements with existing GIS, SCADA, and CMMS systems; they fail to model total cost of ownership beyond year one; or they select a platform optimised for industrial manufacturing environments that was never designed for the distributed, heterogeneous, and often low-connectivity environments that define civil infrastructure monitoring. Each failure mode has a predictable consequence — and understanding them before the evaluation process begins is the most valuable preparation an infrastructure programme manager can do.
Demo Environment Bias
Vendor demo environments feature curated sensor estates, pre-cleaned data, and stable connectivity. Real infrastructure monitoring involves legacy sensors, protocol heterogeneity, intermittent field connectivity, and data quality gaps — conditions that expose platform architectural weaknesses invisible in any vendor demo.
Integration Underestimation
Infrastructure organisations already operate GIS platforms, SCADA systems, and CMMS tools. Selecting an IoT platform with weak or schema-rigid integration APIs forces expensive custom integration work that consumes the platform's projected ROI within 12–18 months of deployment.
Year-One TCO Focus
Platform licence costs in year one routinely represent 20–30% of true 5-year TCO. Integration development costs, data storage scaling, sensor onboarding fees, and professional services for model configuration compound rapidly — and are rarely visible in the initial vendor proposal without direct interrogation.
Manufacturing-OT Platform Mismatch
Many leading IoT platforms are architected for factory floor operational technology — high-speed, wired, low-latency environments with homogeneous sensor types. Civil infrastructure monitoring involves LoRa, NB-IoT, solar-powered remote sensors, sporadic connectivity, and asset lifespans measured in decades rather than years.
Scalability Assumptions
A platform that performs well with 50 sensors on a pilot bridge behaves differently managing 5,000 sensors across a regional infrastructure portfolio with multi-tenant data governance requirements. Scalability must include data volume, concurrent user load, and multi-site asset hierarchy management — not just sensor connection count.
Security and Compliance Gaps
Critical infrastructure IoT platforms operate in environments with stringent cybersecurity requirements — NIS2 in Europe, CISA guidance in the US, and sector-specific data sovereignty obligations. Platforms without end-to-end encryption, role-based access control, and auditable data residency documentation fail regulatory due diligence post-procurement.
The 8-Criteria Framework for Selecting an IoT Platform for Infrastructure Asset Management
The following evaluation framework is structured to address the failure modes above — providing the specific questions and evaluation criteria for each dimension that matter most in civil infrastructure IoT deployments. For each criterion, a red flag section identifies responses or platform behaviours that should signal concern during vendor evaluation. To walk through this framework applied to iFactory's platform architecture, book a structured platform evaluation session.
Sensor Protocol and Connectivity Support
The platform must natively support the full range of protocols used in your sensor estate — including OPC-UA, Modbus RTU/TCP, MQTT, LoRaWAN, NB-IoT, 4G/5G, and legacy 4–20mA analogue inputs via edge gateways. Evaluate the platform's edge device ecosystem and its ability to ingest data from multiple simultaneous protocols without requiring bespoke integration code for each sensor type. Red flag: Vendor requires custom SDK development for each new sensor type, or does not support LPWAN protocols for remote field deployments.
GIS-Native Asset Management Architecture
Infrastructure asset management is inherently spatial — assets have locations, networks have topologies, and condition data must be interpreted in geographic context. Evaluate whether the platform operates with a GIS-native data model (not just a GIS visualisation layer bolted onto a non-spatial database). Look for native integration with Esri ArcGIS, QGIS, or OpenStreetMap, and the ability to build asset hierarchies that reflect real network topology. Red flag: Platform treats GIS as a separate module requiring manual data sync rather than as the primary spatial context for all operational data.
CMMS and SCADA Integration APIs
The IoT platform does not replace your CMMS or SCADA — it must integrate bidirectionally with them. Evaluate the REST API surface, the availability of pre-built connectors for Maximo, SAP PM, Infor EAM, and OSIsoft PI, and whether work order creation from IoT alerts is handled as a configured workflow or requires custom development. The platform should push AI-generated maintenance alerts as structured work orders to your CMMS without manual intervention. Red flag: Integration to existing systems requires a separate professional services engagement not included in the platform licence.
Scalability: Data Volume, Multi-Site and Multi-Tenant Architecture
Request documented evidence of the platform's largest active deployment by sensor count, continuous data event rate (events per second), and organisation size. Evaluate the multi-site architecture — specifically whether multi-tenancy allows regional teams access only to their asset sub-portfolios within a single platform instance. Red flag: Vendor cannot provide reference deployments at 10× your planned initial scale, or multi-tenancy requires separate platform instances rather than role-based access within a single architecture.
AI and Machine Learning Model Architecture
Evaluate whether ML models are pre-trained and asset-class generic, or whether the platform supports model training on your specific asset's historical operational data. Generic models frequently underperform on site-specific infrastructure assets with non-standard operating regimes. Assess whether the platform provides model explainability outputs — the sensor evidence that generated a recommendation — essential for engineering teams to trust and act on AI alerts. Red flag: Platform's AI outputs are black-box recommendations without explainable feature importance or confidence intervals.
Data Security, Residency and Cybersecurity Compliance
Evaluate the platform's encryption standards (TLS 1.2+ in transit, AES-256 at rest), its data residency options (in-country cloud hosting for regulated assets), penetration testing cadence, and compliance certifications (ISO 27001, SOC 2 Type II). For defence-adjacent or national security infrastructure, evaluate air-gapped or private cloud deployment options. Red flag: Single-region cloud hosting without in-country data residency options for regulated infrastructure assets.
5-Year Total Cost of Ownership Modelling
Require vendors to provide a structured 5-year TCO estimate covering: platform licence (per-asset or per-sensor pricing at your target scale), data storage and retention costs at your projected event volume, edge gateway hardware, professional services for model configuration and sensor onboarding, training, and annual support SLA costs. Compare vendors on TCO at your 3-year scale, not year-one pricing — the delta between vendor proposals typically doubles or triples when modelled at operational scale. Red flag: Vendor refuses to provide TCO modelling or quotes only year-one platform licence without storage or professional services.
Vendor Viability and Infrastructure Sector Depth
Evaluate the vendor's customer retention rate, infrastructure-sector reference site count, and the availability of dedicated infrastructure domain expertise within their customer success team. For long-term infrastructure programmes, assess vendor lock-in exposure: evaluate open data export formats and API availability that would allow platform migration without data loss. Red flag: Fewer than 5 deployable reference sites in civil infrastructure, or no customer success team with infrastructure engineering credentials.
IoT Platform Vendor Scorecard: How iFactory Rates Across All 8 Criteria
The scorecard below applies the 8-criteria framework to iFactory's infrastructure AI platform — providing a transparent self-assessment across each evaluation dimension. We encourage infrastructure procurement teams to request equivalent scorecards from all shortlisted vendors, with supporting evidence for each rating. To validate any criterion below with deployment evidence from active iFactory infrastructure programmes, request a technical due diligence session.
"We evaluated five IoT platforms over a six-month process before selecting iFactory. Three of the others failed on the CMMS integration criterion — they all required custom API development that would have consumed roughly half our first-year implementation budget. One failed on data residency: our regulatory framework requires in-country data storage and they couldn't provide it. iFactory was the only vendor that came in with a structured TCO model for five years, pre-built connectors to our Maximo environment, and a reference site in a comparable national roads authority deployment. That evidence base made the procurement decision defensible to our board."
A Structured 5-Stage IoT Platform Selection Process for Infrastructure Programmes
The evaluation framework above defines what to assess — but the selection process also needs to be structured to avoid common procurement pitfalls. The five-stage process below is designed for infrastructure organisations running formal procurement processes for IoT platform investment decisions of £500K+ total programme value.
Define Requirements Against Your Specific Asset Portfolio
Before issuing any vendor briefing, develop a requirements specification anchored to your actual asset estate — including the asset types to be monitored, the sensor protocols currently deployed or planned, the specific CMMS and GIS systems requiring integration, and the regulatory frameworks governing data security. Generic RFP requirements attract generic platform responses; asset-specific requirements force vendors to demonstrate real-world deployment fit.
Issue an RFI With the 8-Criteria Scorecard as the Response Template
Structure your RFI to require responses against each of the eight evaluation criteria — with supporting evidence (reference sites, technical specifications, compliance certificates) required for each. This prevents vendors from submitting glossy capability brochures in lieu of substantive capability evidence and makes comparative scoring straightforward during RFI evaluation.
Shortlist and Conduct Reference Site Visits
For shortlisted vendors (typically 2–3), require reference site visits to comparable infrastructure deployments — not vendor-curated customer panels, but live operational deployments where your team can speak directly with the asset owner's engineering and data teams about real-world platform performance, integration experience, and vendor support quality.
Pilot on a Representative Asset With Your Own Sensor Data
Before final selection, require shortlisted vendors to deploy a time-limited pilot on one of your actual asset sites — using your existing sensor protocols and generating work orders in your live CMMS. A 90-day pilot on a single infrastructure asset exposes integration complexity, data quality handling, and real-world platform performance issues that no demo environment can simulate.
Negotiate TCO and Contractual Exit Rights Before Commitment
Final commercial negotiation should include: 5-year TCO commitments with pricing caps at contracted scale thresholds; data portability commitments (full data export in open formats at contract end); SLA terms with financial penalties for uptime and alert latency breaches; and contractual rights to audit model performance against agreed KPIs. Vendor lock-in risk is most mitigatable at contract signature — not after 18 months of data accumulation on a proprietary platform.
5-Year TCO Benchmark: IoT Platform Cost Components for Infrastructure Programmes
The table below provides a benchmark cost component breakdown for 5-year IoT platform TCO in a medium-scale infrastructure monitoring programme (500 sensors, 50 assets, 3 sites). Platform licence costs rarely represent more than 30% of true programme TCO. To get a TCO model specific to your programme parameters, book a cost modelling session.
| TCO Component | % of 5-Year TCO | Risk if Underestimated | iFactory Approach |
|---|---|---|---|
| Platform Licence (SaaS) | 25–35% | Medium | Per-asset pricing, capped scale tiers |
| Integration Development | 20–35% | High | Pre-built connectors, no custom SDK |
| Data Storage & Retention | 10–20% | High | Tiered storage, cold archive option |
| Edge Hardware & Installation | 10–15% | Medium | Vendor-neutral gateway support |
| Model Configuration & Training | 5–15% | High | Included in onboarding programme |
| Ongoing Support & SLA | 10–15% | Medium | Tiered SLA with infrastructure domain CSM |
| Training & Change Management | 5–10% | Low | Included in platform onboarding |
Ready to Evaluate IoT Platforms for Your Infrastructure Programme? Start With iFactory.
Apply this 8-criteria framework to iFactory's infrastructure AI platform — with live reference deployments, structured TCO modelling, and pre-built CMMS and GIS integration connectors ready for your due diligence process.
Frequently Asked Questions: Selecting an IoT Platform for Infrastructure Asset Management
What is the single most common reason IoT platform deployments underperform in infrastructure programmes?
Integration failure is the most common cause. Infrastructure organisations typically operate a complex existing technology stack — GIS platforms, SCADA systems, CMMS tools, and financial systems — and the IoT platform selected is rarely evaluated rigorously on its real-world integration behaviour with these systems. When integration requires custom API development or creates synchronisation latency between the IoT platform and the CMMS, the operational benefit of AI-generated maintenance alerts is significantly eroded. Platforms with pre-built, tested connectors to the major infrastructure CMMS and GIS environments consistently outperform those requiring custom integration development.
Should we use a general-purpose IoT platform or an infrastructure-specific platform?
For large, complex infrastructure portfolios — bridges, water networks, dams, tunnels — infrastructure-specific platforms consistently outperform general-purpose IoT platforms over a 3–5 year horizon. General-purpose platforms require significant configuration and professional services investment to adapt to civil infrastructure data models, connectivity environments, and asset management workflows. Infrastructure-specific platforms arrive with pre-configured asset hierarchies, sensor ontologies for common infrastructure monitoring use cases, and CMMS integration that reflects infrastructure maintenance workflows — reducing time-to-value and ongoing customisation overhead substantially.
How should we evaluate an IoT platform's AI and predictive analytics capabilities?
Evaluate three dimensions: model architecture (are models pre-trained and generic, or does the platform support training on asset-specific historical data?), explainability (does the platform provide feature importance evidence alongside recommendations, so engineers can evaluate and trust the AI output?), and performance validation (can the vendor provide documented model accuracy metrics — precision, recall, false positive rate — from comparable deployments?). Be wary of vendors who cannot provide performance data from live infrastructure deployments rather than controlled benchmark environments.
What cybersecurity requirements should an IoT platform meet for critical infrastructure use?
At minimum: TLS 1.2 or higher for all data in transit; AES-256 encryption at rest; role-based access control with multi-factor authentication; ISO 27001 certification or SOC 2 Type II attestation; documented penetration testing on an annual or bi-annual cadence; and in-country data residency options for government-regulated assets. For assets within scope of NIS2 (EU) or equivalent critical infrastructure protection frameworks, the platform must also support audit logging of all access events and provide documented incident response procedures.
What is a realistic 5-year total cost of ownership for an IoT infrastructure monitoring platform?
For a medium-scale programme (500 sensors, 50 assets, 3 sites), 5-year TCO typically ranges from $800K to $2.5M depending on integration complexity, data volume, and SLA tier. Platform licence typically represents 25–35% of this total. Integration development (if not pre-built), data storage at scale, and professional services for ongoing model optimisation collectively represent 50–60% of true programme cost — making vendor claims based on licence pricing alone highly misleading. Always require 5-year TCO modelling as a mandatory deliverable from shortlisted vendors before procurement commitment.
How do we avoid vendor lock-in when selecting an IoT platform for long-term infrastructure asset management?
Four contractual protections reduce lock-in risk significantly: (1) require open data export in standard formats (JSON, CSV, Parquet) at contract end without data transformation costs; (2) negotiate API access that allows third-party tools to query your data without vendor mediation; (3) include a model portability clause — trained ML models should be exportable in standard formats (ONNX, PMML); and (4) require data deletion and confirmation within 30 days of contract termination. These protections are most effectively negotiated before contract signature, not after deployment has created commercial leverage for the vendor.
How long does an IoT platform pilot typically take for an infrastructure asset management programme?
A meaningful pilot — one that exercises the platform's sensor ingestion, data quality handling, CMMS integration, and AI alert generation on a real asset — typically requires 60–120 days. Platform connection and initial data flow usually stabilises within 2–4 weeks; AI model calibration and alert threshold validation requires 4–8 weeks of live operational data; and CMMS integration testing with a realistic mix of alert types requires a further 2–4 weeks. Pilots shorter than 60 days rarely expose the data quality and integration edge cases that determine long-term platform performance.
Does iFactory's platform support open-source sensor hardware, or does it require proprietary hardware?
iFactory's infrastructure AI platform is explicitly hardware-agnostic — it supports sensor data ingestion from any hardware that transmits via standard protocols (OPC-UA, MQTT, Modbus, REST API, LoRaWAN, NB-IoT, 4G/5G). The platform includes pre-configured data parsers for the most commonly deployed infrastructure sensor manufacturers, and new hardware types can be onboarded through a configuration wizard without SDK development. This vendor-neutral approach protects infrastructure owners from hardware lock-in and allows the most cost-effective sensor selection for each monitoring use case and site connectivity environment.